Protection Hazard: High Exploitation Amount: Quick CVSS Rating: 9.9 / 7.7 Vulnerability: Privilege Escalation, SQL Injection Patched Edition: 4.1.5.3
Very last week, stability researcher at Automattic Marc Montpas lately discovered two significant stability vulnerabilities within one particular of the most preferred Seo plugins utilised by WordPress site owners: All in One particular Web optimization. The plugin is employed by extra than a few million websites and if still left unpatched could bring about some critical complications for WordPress customers.
The Details
Both equally vulnerabilities call for that the attacker have an account on the web-site, but the account could be as reduced-degree as a subscriber. WordPress web sites by default permit any person on the world wide web to create an account. By default new accounts are ranked as subscriber and do not have any privileges other than crafting feedback. However, specified vulnerabilities, these as the types just learned, permit these subscriber end users to have vastly much more privileges than they have been supposed to have. When exploited in tandem, these two safety holes make it possible for an attacker to just take in excess of an unpatched WordPress site.
Authenticated Privilege Escalation
The first concern found with this plugin is fascinating, and can be exploited by merely shifting a solitary character of a request to uppercase. It affects versions 4.. and 4.1.5.2 of All in Just one Search engine marketing. This plugin has access to a selection of Relaxation API endpoints, but performs a permission look at in advance of executing any commands despatched. This assures that the person has right permissions to instruct the plugin to execute commands. However, All in Just one Seo did not account for the subtle actuality that WordPress treats these Relaxation API routes as case-insensitive strings. Changing a one character to uppercase would bypass the authentication checks altogether.
When exploited, this vulnerability has the functionality to overwrite specific documents in just the WordPress file framework, efficiently giving backdoor obtain to any attacker. This would make it possible for a takeover of the site, and could elevate the privileges of subscriber accounts into admins.
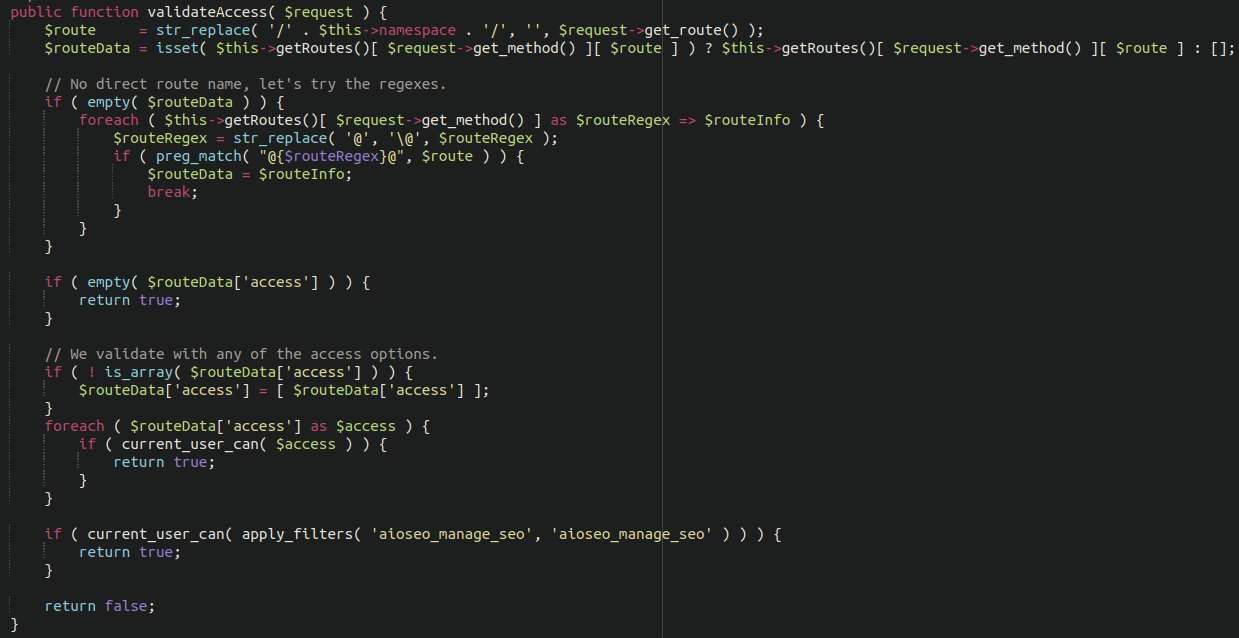
Vulnerable code in All-In-One particular-Search engine optimization WordPress plugin making it possible for for privilege escalation
Authenticated SQL Injection
The 2nd vulnerability found out is present in variations 4.1.3.1 and 4.1.5.2 of this plugin. There is a certain endpoint located right here:
/wp-json/aioseo/v1/objects
This endpoint isn’t intended to be obtainable by reduced-degree accounts. Nonetheless, considering that the preceding vulnerability explained authorized for privilege escalation, the attackers could 1st elevate their privileges and then execute SQL commands to leak delicate facts from the databases, including consumer qualifications and admin information and facts.
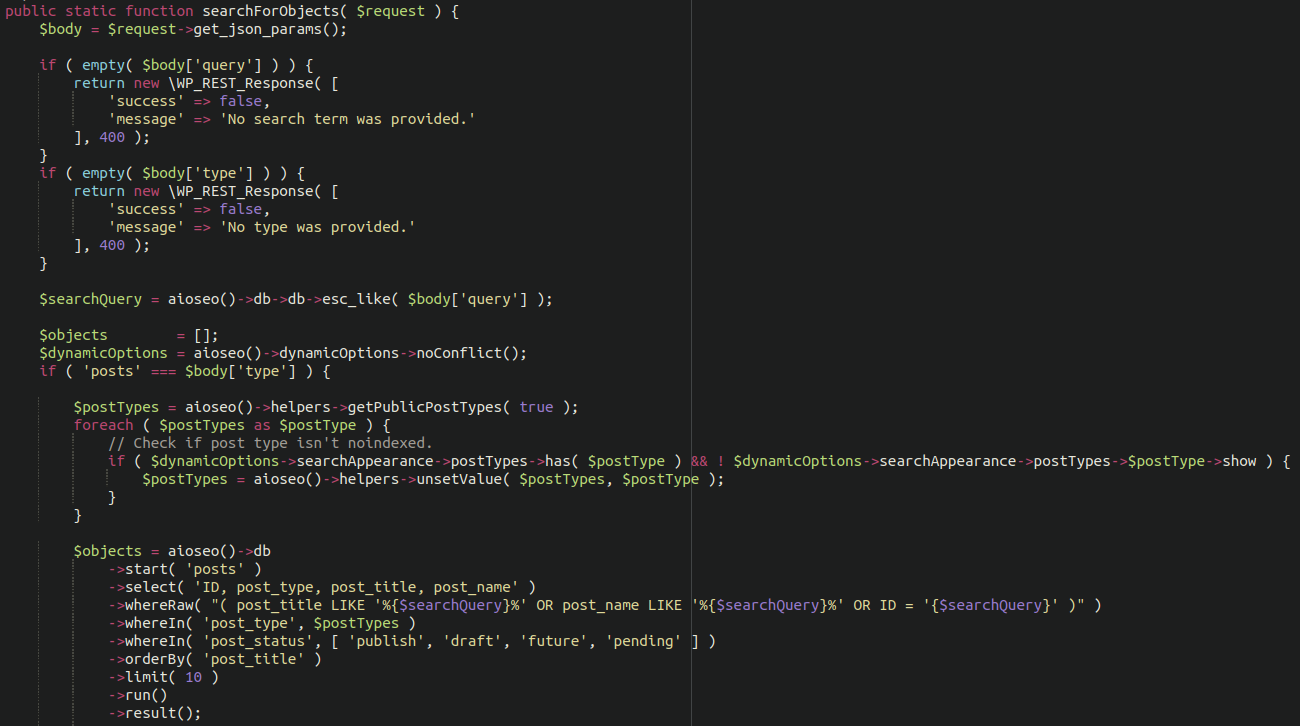
Vulnerable code in All-In-A person-Web optimization WordPress plugin enabling for SQL injection
In Conclusion
If your internet site is making use of All in A person Seo be sure to update to the most latest edition as shortly as doable! You will also want to overview the administrator people current on your site. Remove any suspect buyers that you do not recognise, and for good measure improve all administrator account passwords. It is also prudent to increase some more hardening to your administrator panel.
Consumers of our firewall are protected versus these vulnerabilities. Although we generally endorse updating out of day plugins to the most recent model, notably in cases such as these where safety challenges are current!
